Understand how to evaluate TCO in electronic security projects, including CAPEX, OPEX, integration, cybersecurity, compliance, and long-term sustainability.
Check it out!
TCO in electronic security projects, or Total Cost of Ownership, is one of the most relevant factors when investing in an integrated electronic security system. Understanding it is fundamental to guide technical, financial, and operational decisions throughout the entire life cycle of systems such as video monitoring, access control, alarms, communication networks, and integrated interfaces. Proper TCO evaluation allows managers, engineers, and designers to understand the factors that directly and indirectly influence both the initial investment and the recurring expenses related to operation, maintenance, and technological upgrading of security solutions. The search for maximum return on investment and operational efficiency is directly associated with mastery of TCO calculation methodologies, especially when considering the normative specificities present in structured and vertically integrated physical and logical security projects.
In this article, the following topics are analyzed in a structured manner: the technical foundations of TCO in electronic security systems; methodologies for its correct estimation; the critical factors that most affect cost throughout the life cycle; practical examples that break down the main recurring costs; and recommendations for systemic TCO management based on applicable national and international standards, such as ABNT NBR IEC 62676 for video monitoring systems and other normative references in the sector. This content aims to provide technical support for sound decisions in projects, technical proposals, and security asset management strategies.
Keep reading.
[elementor-template id=”24446″]
Fundamentals of Total Cost of Ownership Applied to Electronic Security
The concept of Total Cost of Ownership goes beyond initial investment, or CAPEX, and encompasses the detailed evaluation of all costs involved throughout the useful life cycle of an electronic security system. This includes direct and indirect expenses, integration costs among different platforms, operation expenses, maintenance, technological upgrades, as well as obsolescence and component disposal issues.
In the context of systems involving multidisciplinary projects such as electrical installations, telecommunications networks, and the integration of multiple systems, such as surveillance, access control, alarm, and fire detection, each with its own peculiarities and normative requirements described in ABNT NBR IEC 62676, NBR 5410, and NBR 14565, among others, TCO analysis involves considering elements such as:
- Physical infrastructure: Structured cabling, electrical power devices, communication networks, racks, and mounting elements;
- Active and passive equipment: Cameras, sensors, controllers, VMS platforms, switches, power supplies, and PoE systems, or Power over Ethernet;
- Software licensing: Management platforms, analytics systems, integration modules, and per-channel licenses;
- Integration and interoperability costs: Interfaces with other systems, such as CCTV, access control, and intrusion, adaptation to different vendors, normative compliance, and customization;
- Implementation services: Engineering, installation, commissioning, training, and document preparation;
- Operation, maintenance, and support: Firmware updates, technical support contracts, continuous training, and spare parts costs;
- Responsible disposal and upgrading: Costs related to planned obsolescence, environmentally correct disposal, and replacement by new technologies.
Careful TCO evaluation makes it possible to identify critical points for cost optimization, risk reduction, and improved system efficiency, directly impacting the longevity and sustainability of the investments made. However, only a company with solid expertise in security design is capable of preparing a project that is truly aligned with the technical and budgetary needs of the client.
This technical and strategic differentiator makes all the difference: choosing a project that includes an economic feasibility study means ensuring that every stage of the solution is appropriate to the client’s purchasing capacity without giving up performance and security. In this way, the investment in project design proves small in comparison with the economic gains produced by a deep and technical TCO analysis, making it a fundamental element for the success and durability of the systems implemented.
Methodology for Estimating TCO in Electronic Security Projects

The methodology for calculating TCO in electronic security projects must adopt a systemic approach, structuring the process into sequential stages involving the survey, categorization, and analysis of all cost components. It is recommended to detail the following blocks:
- Functional Scope Mapping
- Definition of the overall system architecture, including the scope of video monitoring, access control, alarms, and integrations;
- Survey of normative and functional requirements in accordance with ABNT NBR IEC 62676;
- Capital Cost Survey, or CAPEX
- Active and passive equipment, such as cameras, servers, controllers, and power supplies;
- Electrical and logical infrastructure, such as cables, conduits, distribution boards, and switches;
- Software licenses, VMS platforms, and integration modules;
- Development of executive projects, installation services, commissioning, and initial training;
- Operational Cost Survey, or OPEX
- Preventive and corrective maintenance;
- Technical support contracts and firmware and software updates;
- Energy consumption of devices and auxiliary systems, such as UPS, cooling, and PoE systems;
- Normative updates, periodic training, and staff retraining costs;
- Integration and Management Costs
- Interconnection among different systems, such as CCTV, access control, intrusion, and building or industrial automation;
- Compliance requirements for multiple interfaces and technical compatibility analysis;
- Integrated monitoring and adjustment of recording parameters, date and time, and alarm restoration;
- Life Cycle and Obsolescence Analysis
- Projection of technology upgrade costs, component replacement, and environmentally appropriate disposal;
- Periodic evaluation of system effectiveness in the face of new regulatory requirements and technological advances;
By adopting this methodology, the technical manager gains stronger support for decision-making, enabling the preparation of technical-financial decision matrices guided by the best relationship between cost and performance over the projected time horizon.
Structuring TCO Components in Video Monitoring, Access Control, and Integrated Security Systems
In electronic security projects, the breakdown of TCO costs must be carried out according to the subsystems involved. Detailed understanding of each component is indispensable to ensure compliance, performance, and high budget predictability.
1. Video Monitoring, or IP CCTV
- Core equipment: Compatible IP network cameras, video servers, VMS platforms, NVRs and storage, and PoE power devices;
- Infrastructure: Structured cabling, patch panels, outlets, managed switches, electrical protection devices, and UPS;
- Licensing and software: VMS, analytics, integration, and remote monitoring;
- Integration services: Configuration of recording parameters, event management, and interfaces with automation, access control, and alarms;
- Operational costs: Maintenance, periodic updates, integrity analysis, and replacement of cameras and critical components;
2. Access Control
- Controllers and readers: Authentication devices, biometrics, RFID readers, and proximity cards;
- Electrical infrastructure: Power supplies, batteries, backup devices, and redundancy;
- Licensing: Access management platforms and integration modules with building and industrial systems;
- Associated services: Parameterization, access rule programming, and operator training;
- Recurring costs: Updates, credential revalidation, maintenance of authentication devices, and technical support;
3. Integration with Third-Party Systems
- Interface with building automation, industrial systems, environmental sensors, and fire systems;
- Costs related to custom integration development, open protocols such as ONVIF, BACnet, and Modbus, and normative adaptation;
- Consolidated monitoring, response to integrated events, and automation of multi-platform logical responses;
When structuring the budget and planning of an integrated electronic security system, a broad view of these components is fundamental to avoid cost overruns caused by compatibility failures, lack of integration, or accelerated obsolescence.
Main Factors That Drive TCO Variation in Electronic Security Projects
The TCO of electronic security projects can vary significantly due to different technical, operational, and contextual factors. The main determinants are presented below:
- System topology and scope: Distributed systems, multisite architectures, or environments with redundancy requirements exponentially increase infrastructure and synchronization costs;
- Technologies employed: IP-based systems, with use of PoE, make it possible to rationalize physical and energy infrastructure, whereas analog solutions, now practically unviable, tend to result in higher maintenance costs and lower scalability;
- Update and maintenance management policy: Lack of planning for systematic updates of firmware, licenses, and equipment raises corrective costs and reduces system longevity;
- Degree of integration and automation: Systems integrated with building or industrial automation require greater investment in development, interoperability, and customization, affecting both CAPEX and OPEX;
- Normative adequacy and compliance: Meeting ABNT NBR IEC 62676 requirements and international standards may demand additional costs with documentation, audits, and interface validation;
- Physical and logical security policy: Investments in physical protection, network segmentation, and logical access control add implementation and maintenance costs, but increase system efficiency and performance;
- Obsolescence and planned life cycle: Failure to consider component life cycle may lead to premature replacements not anticipated in the original budget, significantly affecting TCO.
Therefore, correct identification and mitigation of these factors must be part of any strategy for planning and monitoring complex electronic security projects.
Technical Standards and Their Influence on TCO Composition
Electronic security projects, whether focused on video monitoring, access control, or system integration, are subject to strict compliance with national and international technical standards. ABNT NBR IEC 62676, for example, defines criteria for the structuring and performance of video monitoring systems. Such requirements directly impact TCO by demanding:
- Implementation of recording, search, playback, and alarm acknowledgment or restoration functions;
- Detailed logging of parameter changes, events, and date and time marks, increasing the complexity of administrative and log systems;
- Interoperability between platforms from different manufacturers, requiring higher investment in integration and conformity testing;
- Comprehensive protection of components and interfaces to ensure systemic integrity and avoid unauthorized access;
- Redundancy strategies, fault detection, and protection against physical and logical tampering;
In addition, requirements for permanent updating of software and firmware, user account management, IP address filtering, and sophisticated authentication mechanisms such as IEEE 802.1X increase both the initial investment and maintenance costs. Technical compliance not only ensures full system operation, but also adds value to the investment by reducing operational, legal, and security risks at interfaces with third-party systems.
Practical Study: TCO Component Breakdown in an IP Video Monitoring Project

Technical Collection – A3A Systems Engineering
To exemplify the application of the TCO concept in real electronic security projects, consider an IP video monitoring system intended for perimeter and internal area protection, with an architecture based on ABNT NBR IEC 62676 and recommendation of PoE devices and centralized management.
Logical and physical infrastructure
- Sizing of PoE switches for centralized power supply, aiming to reduce auxiliary cabling. This results in energy savings, simplified installation, and easier implementation of electrical backup.
- Rack mounting, electrical protection, and accommodation of redundant storage for image recording in accordance with normative requirements and best practices for operational continuity.
Licensing costs
- Investment in VMS platforms, including per-channel licenses, analytics systems, and native integration with access control. Planning must foresee upgrade and expansion costs according to system growth.
Maintenance expenses
- Constant firmware updates and device integrity verification, in addition to planned replacement of cameras and critical components, are mandatory requirements of technical standards.
- Periodic training for operators, ensuring correct operation, rapid incident response, and high system availability.
- Development and maintenance of integration interfaces among heterogeneous systems, such as video monitoring, access control, and building automation, meeting interoperability requirements and full adherence to ABNT NBR IEC 62676.
Costs Related to Data Protection, Cybersecurity, and Network Security
- Data protection compliance: It is indispensable to consider investment in privacy solutions, anonymization, and sensitive data management, establishing clear policies for retention and disposal of images and records.
- Cybersecurity: Costs must include device hardening, network segmentation, firewalls, multifactor authentication, data encryption in transit and at rest, and intrusion monitoring solutions, or IDS and IPS.
- Network security: Fundamental to mitigate invasion risks, which are common in CCTV systems. Planning must foresee periodic audits, password updates, use of VPNs, restriction of remote access, and continuous log monitoring, ensuring resilience against attacks and data leaks.
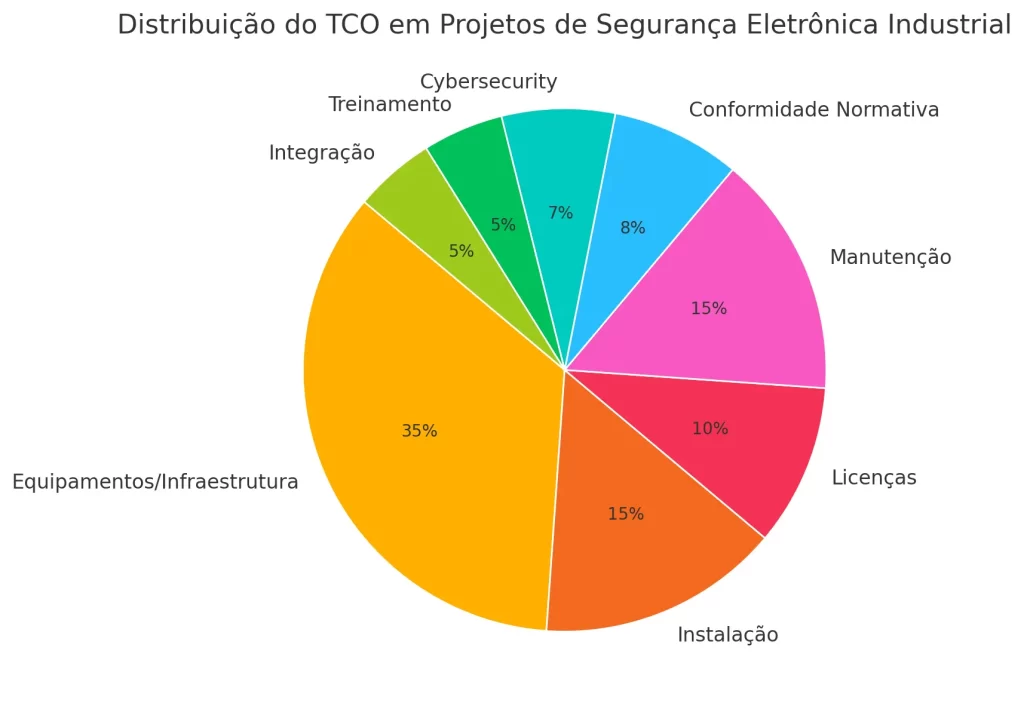
Summary:
When breaking down the TCO of an IP video monitoring project, it becomes evident that efficient cost management depends on adopting sound normative practices, investing in training, and paying rigorous attention to privacy regulation and cybersecurity. These elements not only ensure compliance and performance, but also minimize operational and legal risks, increasing the longevity and sustainability of electronic security systems.
TCO Management: Technical Recommendations for Optimization and Sustainability
To achieve maximum efficiency and financial sustainability in electronic security projects, adoption of the following good TCO management practices is recommended:
- Detailed executive projects: Carry out field surveys and complete executive designs, minimizing sizing errors and emerging costs;
- Careful selection of suppliers and technologies: Prioritize systems compatible with open standards, robust protocols, and native integration, reducing customization costs and supporting progressive upgrades;
- Life cycle management: Prepare plans for technological updating, proactive replacement of components, and continuous team training;
- Permanent monitoring of cost indicators: Implement TCO monitoring tools, establishing periodic metrics to compare actual and projected expenses;
- Predictive maintenance policy: Replace corrective models with strategies based on predictive diagnostics, adding value and longevity to the system;
- Adoption of centrally powered solutions: Use PoE whenever possible, reducing dedicated electrical infrastructure costs and optimizing total system energy consumption;
- Compliance and audit procedures: Ensure continuous normative compliance by reviewing documentation, logical and physical access policies, and conducting regular technical audits;
Such recommendations provide greater stability, reliability, and budget predictability, paving the way for strategic TCO management in medium- and large-scale electronic security systems.
Conclusion
Advanced understanding and efficient management of Total Cost of Ownership in electronic security projects are essential elements for organizations to achieve high standards of security, operational performance, and financial sustainability in their systems. Careful TCO analysis, grounded in technical standards such as ABNT NBR IEC 62676, allows anticipation of risks, intelligent investment planning, and mitigation of hidden costs associated with operation, maintenance, updating, and compliance of integrated systems. Proper balancing between CAPEX and OPEX, combined with evaluation of life cycle, interoperability, and technological updating, generates results directly converted into greater robustness and longevity of the security environment, ensuring adherence to increasingly demanding normative and operational requirements. In this way, application of the TCO concept is consolidated as an indispensable tool for engineers, managers, and decision-makers in the segment, optimizing resources and aligning technology, security, and efficiency.
Final Considerations
Based on the explanations and technical recommendations presented, it is reinforced that the analysis of Total Cost of Ownership must be an intrinsic part of the planning, implementation, and management of any electronic security project. We thank you for reading this technical article and invite all professionals, clients, and partners to follow A3A Systems Engineering on our social networks for continuous updates on strategic topics in security, technology, and applied engineering.
Also read:
Total Cost of Ownership of a Video Monitoring System
Cybersecurity in Video Monitoring Systems
Main Applications of Video Analytics
Frequently Asked Questions
1. What is TCO and why should it be considered in IP video monitoring projects?
TCO, or Total Cost of Ownership, encompasses all direct and indirect costs of the system, including acquisition, deployment, maintenance, training, licensing, security, updates, and integration. A careful TCO evaluation makes it possible to optimize investments, prevent hidden costs, and ensure system longevity and efficiency.
2. Which costs are commonly neglected in the TCO of video monitoring systems?
Expenses related to software licenses, preventive maintenance, security updates, team training, replacement of obsolete equipment, integration with other systems, and compliance with data protection regulation are often underestimated.
3. How does data protection regulation affect video monitoring projects?
Data protection regulation requires that images and data collected by CCTV systems be handled securely, with retention, disposal, and restricted-access policies, as well as due consideration of data subject rights. The project must foresee anonymization solutions, access control, audit records, and documentary compliance.
4. How can a CCTV project fully comply with data protection regulation?
In addition to restricting access, it is essential to train operators, document processes, maintain audit records, and adopt solutions such as anonymization in sensitive areas, ensuring continuous compliance.
5. Which cybersecurity practices are essential to protect CCTV systems against attacks?
Constant firmware updates, use of strong passwords, network segmentation, firewalls, data encryption, multifactor authentication, access monitoring, audits, and periodic penetration testing are indispensable to system security.
6. What is the impact of failing to invest in cybersecurity for CCTV systems?
Lack of security measures can result in intrusions, image manipulation, data leaks, and even system paralysis caused by attacks, leading to financial losses and legal risks.
7. Why is network security so important in IP video monitoring projects?
Network-connected CCTV systems are frequent targets of attacks that can result in intrusion, image hijacking, or sensitive data leaks. A secure network protects system integrity, information privacy, and organizational reputation.
8. How can IP video monitoring be integrated with access control and building automation systems?
Efficient integration depends on the use of open standards, such as ONVIF, compatible software, and unified security and update policies for all interconnected systems.
9. Does investing in an economic feasibility study really reduce the final project cost?
Yes. A technical and economic feasibility study identifies tailored solutions, avoids unnecessary spending, minimizes risks, and guides the choice of the best equipment and technologies according to budget, increasing return on investment, or ROI.
10. How should maintenance and updating be planned to ensure long-term compliance and performance?
Include routines for software updates, review of security policies, scheduled replacement of equipment, continuous training, and regular integrity tests. Document all actions for management and audit purposes.
11. How does monitoring automation contribute to TCO and security?
Automation with video analytics and intelligent alarms reduces operational costs, increases efficiency, improves incident response time, and decreases the need for human intervention.
12. What is the importance of documenting all system processes and configurations?
Detailed documentation facilitates maintenance, audits, updates, and knowledge transfer, and is essential for compliance with technical standards and data protection requirements.
13. Which extra measures increase the useful life and performance of a CCTV system?
Choosing high-quality components, ensuring proper installation, protecting the environment with racks and stable power, maintaining preventive maintenance contracts, and periodically updating the systems maximize system reliability and longevity.
14. Which technological trends should be considered in IP video monitoring projects?
Trends such as artificial intelligence for video analysis, integration with IoT systems, use of high-resolution cameras, cloud storage, and embedded cybersecurity solutions are transforming the efficiency and scope of CCTV systems.
15. How should an engineering company be chosen to prepare an efficient electronic security project?
The choice should consider proven experience in similar projects, mastery of applicable technical standards, the ability to provide customized and integrated solutions, a history of compliance with privacy and cybersecurity requirements, as well as qualified technical support and commitment to a detailed TCO study to ensure economic viability and operational efficiency.

