The Dark Web is a hidden part of the internet accessible only through specific software and protocols that guarantee anonymity, such as the Tor browser. Unlike the surface web (indexed by search engines) and the deep web (non-indexed content), the dark web is known for its high level of privacy and anonymity, being used for […]
Check it out!
The Dark Web is a hidden part of the internet accessible only through specific software and protocols that guarantee anonymity, such as the Tor browser. Unlike the surface web (indexed by search engines) and the deep web (non-indexed content), the dark web is known for its high level of privacy and anonymity, being used for both legitimate and illicit purposes. In this article, learn what the Dark Web is, how it works, the risks involved, and the best practices for protecting individuals and businesses.
The Dark Web constitutes a set of overlay networks, characterized by anonymity and the use of advanced cryptographic protocols, allocated in layers above the TCP/IP model, aiming to conceal identities, routes, and accessed content. These infrastructures are built upon anonymization mechanisms, such as onion routing, and accessed via dedicated software, enabling untraceable communications between clients and servers, outside the scope of conventional browsers and search engines. The central motivation for the development and adoption of these networks includes reinforced privacy, censorship resistance, and protection against mass surveillance, introducing growing challenges to cybersecurity, governance, and organizational compliance.
In this article, we present a comprehensive and technically detailed analysis of the Dark Web, covering its definition, distinctions from the Deep Web and Surface Web, network architecture, access methods, involved protocols, anonymization mechanisms, legitimate and illicit applications, main threats and risks, security implications for corporate projects, and technical standards related to mitigation and monitoring. The content is intended for engineering professionals, information security specialists, and risk managers seeking advanced understanding of the topic.
Check it out!
[elementor-template id=”24446″]
What is Surface Web, Deep Web and Dark Web?
Technical illustration of the different internet layers, highlighting the Dark Web’s position, its anonymity elements, encryption, and risks for corporate environments.
Source: A3A Systems Engineering.
To understand the Dark Web, it is essential to outline the distinction between the levels of the Web:
| Characteristic | Surface Web | Deep Web | Dark Web |
|---|---|---|---|
| Visibility | Indexed by conventional search engines (Google, Bing, etc.) | Not indexed by search engines; requires specific permissions | Not indexed, restricted and anonymized access |
| Access | Public and unrestricted via traditional browsers | Controlled: requires authentication, login, or specific configurations | Restricted: requires dedicated software (e.g., Tor, I2P) |
| Content | Institutional portals, public websites, blogs, and open pages | Corporate databases, internal systems, emails, and confidential documents | Anonymous communication services, marketplaces, specialized forums (legitimate and illicit) |
| Anonymity Level | No anonymity, access and browsing information are traceable | Partial, depending on system configuration and permissions | High, infrastructure designed to ensure anonymity and secrecy |
| Legality | Fully legal content and access | Legal, except if associated with illicit practices or unauthorized use | Depends on use and accessed content; there are both legitimate and illicit uses |
| Examples | www.a3aengenharia.com.br, news portals, government agency websites | Corporate intranet, online banking systems, restricted academic environments | .onion addresses, whistleblowing services, protected communication channels |

Source: A3A Systems Engineering.
- Surface Web: The visible layer, indexed by search engines (e.g., websites accessible via standard HTTP/HTTPS).
- Deep Web: Encompasses content not indexed by conventional search engines, including protected databases, restricted system areas, and websites behind authentication, without necessarily implying anonymity or illegality.
- Dark Web: A subset of the Deep Web, composed of websites and services accessible only through specific protocols and software (such as TOR and I2P), designed for total anonymity and encrypted communication. Services located on the Dark Web are not only invisible to search engines but are also beyond the reach of traditional browsers, requiring their own infrastructure for anonymous routing.
Structurally, the Surface Web corresponds to a minority of the total data space, while the Deep and Dark Web encompass content that is mostly untraceable by traditional mechanisms. On the Dark Web, the concept of “overlay network” prevails, forming infrastructures overlaid on the common Internet, with non-trivial authentication and restrictive access mechanisms based on consent or client configuration.
To deepen your understanding of the different internet layers, also read our article on Deep Web: Everything you need to know about the hidden side of the Internet
How the Dark Web’s Underlying Architecture and Infrastructure Works
The Dark Web’s infrastructure is based on overlay networks, aggregated over the traditional TCP/IP architecture. Multi-layer anonymization protocols are implemented — with emphasis on onion routing, the primary enabling technology of the TOR (The Onion Router) network. Other technologies, such as I2P (Invisible Internet Project), follow similar principles of routing through cryptographic layers (garlic routing). These networks are accessible only through specialized software that encapsulates and routes IP packets through multiple nodes, eliminating direct correlation between client, server, and requested content.
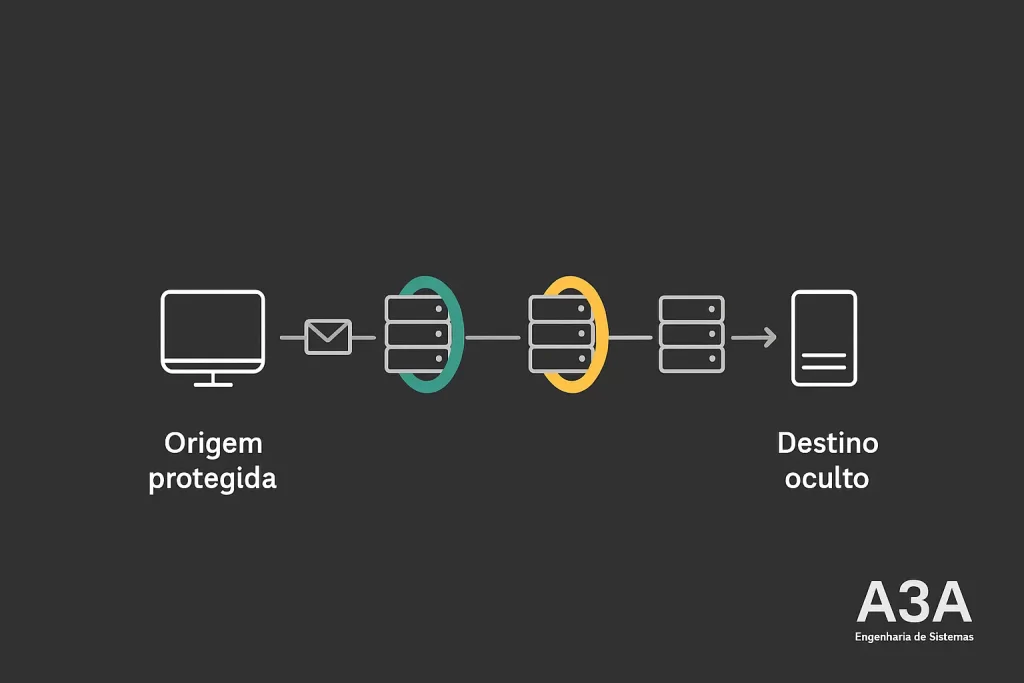
Didactic animation demonstrating how data travels through multiple intermediate nodes, with encryption layers being removed at each stage, ensuring anonymity between origin and destination.
Source: A3A Systems Engineering.
- Onion Routing: Each packet travels through a chain of intermediate servers (nodes), encrypted in multiple layers. Each node removes only its “layer” of encryption, knowing only the previous and next node, never simultaneously knowing the origin or final destination.
- FW and Proxies: Local client configurations involve redirecting browsing traffic to anonymous proxies, with all traffic encapsulated in specific protocols.
- Layers over TCP/IP: The anonymization logic operates above TCP/IP transport, leveraging addressing but overlaying multiple encrypted circuits, typically via non-standard ports and hidden addresses (e.g., ‘.onion’ domains).
The overlay architecture implies challenges for monitoring and inspection, as it fragments and distributes the data flow across different jurisdictions and platforms.
Main Protocols and Software for Accessing the Dark Web
Accessing the Dark Web requires the use of software specifically designed to operate on anonymous overlay networks. Among the main ones are:
- TOR (The Onion Router): A widely disseminated solution for anonymization, accessible to the public through specialized browsers. It uses onion routing, where each web request traverses multiple servers, each decrypting only what is necessary for forwarding.
- I2P (Invisible Internet Project): Implements garlic routing, combining multiple anonymous messages into aggregated packets, making correlation and traffic analysis difficult. It operates with its own addressing infrastructure and dedicated clients.
These software redirect browser or application traffic through anonymous networks, hiding the real source/destination IP and making forensic identification of the user and server highly complex. Communications adopt end-to-end encryption layers, with intensive use of adapted TLS and cryptographic variants to prevent data interception and manipulation.
Access to hidden addresses generally occurs through specific URLs (e.g., ‘.onion’ domains), which have no public record in conventional DNS, requiring the use of distributed directories and exclusive resolution methods.
How Does the Dark Web Ensure Anonymity and Privacy?
The foundation of the Dark Web lies in anonymization mechanisms. Onion routing ensures that each network element knows only the next node, enormously hindering the traceability of communications flow. To ensure additional privacy, the following techniques are employed:
- Multi-Layer Encryption: Each request and response travels protected by multiple layers of encryption, ensuring end-to-end confidentiality.
- Decentralized Proxy Network: Traffic never follows the same IP pointer path, mitigating risks of correlation and flow analysis attacks.
- Resilience Against Sniffing and Spoofing: Using robust encryption to prevent packet interception and modification by malicious agents or third-party-controlled actors.
This technological framework significantly hinders the identification of activities and users, being designed to resist not only censorship but also advanced attempts at surveillance and access blocking.
Main Uses and Applications of the Dark Web (Legal and Illicit)
While the Dark Web offers resources for anonymity and privacy protection — essential, for example, for dissidents in oppressive regimes or investigative professionals — its architecture is also used for the operationalization of illicit activities, since it hinders legal enforcement and oversight.
- Legitimate applications: Anonymous communication, secure journalism, sharing sensitive information under risk, academic research, freedom of expression protection, and resistance to surveillance regimes.
- Illicit uses: Illegal commerce (weapons, drugs, personal data, malware), hacker forums, digital contraband trafficking, cyber attack service exchanges, dissemination of prohibited content, and money laundering schemes.
The diversity of applications and technical accessibility create a convergence zone between legitimate rights to privacy and the risks of supporting structured criminal activities.
Dark Web Risks: Threats, Fraud and Dangers of Access
The risks of accessing and browsing the Dark Web can be classified into multiple domains:
- Exposure to Cyber Threats: High frequency of malware, spear phishing attacks, ransomware, malicious scripts, and exploits on pages and services hosted on these networks.
- Sensitive Data Capture: Possibility of credential leaks, corporate data exposure, and asset compromise if devices are inadvertently infected or used without proper technical barriers.
- Legal Accountability: Inadvertent browsing or access to illicit content can expose individuals and organizations to legal risks of classification as virtual crimes, even without intent.
- Fraud and Extortion: Hubs for organizing financial fraud, extortion schemes, and auctions of confidential corporate information.
- Operational Risk: Actions by malicious entities targeting entry points in corporate environments, with targets on VPNs, proxies, endpoints, and third-party networks connected insecurely.
- Advanced Vectors: Use of reverse proxy techniques and tunneling for lateral propagation in internal networks and stealthy data exfiltration.

Source: A3A Systems Engineering.
Access without adequate protection can also result in device seizure by judicial entities, loss of system integrity, and exposure of employees to recruitment or manipulation attempts by digital criminal organizations.
Technical Summary:
- Greatest risk = exposure to malware and data leaks
- Companies need restrictive policies and continuous monitoring
- Compliance with standards (ISO/IEC, LGPD) is a differentiator
⚠️ Warning:
Accessing the Dark Web, even for research or curiosity purposes, can expose professionals and companies to legal and technical risks, including legal liability, cyber attacks, and sensitive data leaks. Always consult information security specialists before any unconventional access.
Dark Web in Businesses: Risks and Impacts for Corporate Environments
Companies face significant risks by allowing or neglecting Dark Web access in their environments. The main implications include:
- System Vulnerabilities: Outdated systems, misconfigured devices, and lack of access controls can serve as entry points for threats originating from the Dark Web.
- Monitoring and Detection: Need for Intrusion Detection Systems (IDS) and Endpoint Detection and Response (EDR) to identify suspicious activities, such as unusual traffic, connections to unconventional domains, and anomalous code execution.
- Access Control Policies: Implementation of strong authentication mechanisms (multi-factor), privilege segregation, and rigorous use of logs for traceability.
- Data Protection: Emphasis on encryption practices, Data Loss Prevention (DLP), and segregated offline backup to prevent leaks and ransomware.
- Training and Capacity Building: Continuous training of teams in identifying social engineering attacks and the concrete dangers of anonymous networks.
Technical standards such as ABNT NBR IEC 62676-1-1:2019 and corporate security frameworks recommend regular audits, attack simulations, and systematic inspection of backup and record integrity.
How to Monitor, Mitigate and Respond to Dark Web Threats
Monitoring risks from the Dark Web requires:
- Adoption of Firewalls and Network Segmentation: Limiting access points, establishing isolation perimeters, and monitoring packets to identify traffic associated with anonymous proxies.
- Audits and Penetration Testing: Periodic execution of vulnerability assessments and intrusion tests based on threat scenarios conveyed through anonymous networks.
- Backup and Retention Policies: Rigorous maintenance of backup and restore routines, buffer controls, and segregated backup systems, in accordance with requirements defined in technical standards.
- Log Integration and Event Analysis: Centralized logging of interconnections, failure monitoring, and automated responses in cases of detection of suspicious communication with typical Dark Web domains.
- Incident Procedures: Defined incident response structure, with qualified teams for rapid analysis and mitigation of damage caused by unauthorized access or system infection.
All these processes, combined with compliance with regulatory requirements and security recommendations, provide a robust defense posture in sensitive environments.
It is essential to adopt segregated backup policies as recommended by ISO/IEC 27002 and to conduct periodic audits based on NIST frameworks for rapid incident detection and response.
Compliance and Digital Governance Against the Dark Web
Best practices for security and risk management related to the Dark Web are aligned with international technical standards, such as ABNT NBR ISO/IEC 27001 (Information Security Management), ISO/IEC 27005 (Risk Management), and national legislation such as the LGPD. Additionally, recommendations from CERT.br and NIST frameworks reinforce protection, monitoring, and incident response policies involving anonymous environments.
The positioning towards the Dark Web in the business and institutional context depends on reinforced compliance policies, risk management, and alignment with regulations such as the General Data Protection Law (LGPD), ISO/IEC 27005, and ISO/IEC 31000. It is recommended:
- Risk Mapping: Preparation of technical impact reports (Data Protection Impact Assessment), considering, in addition to the logical environment, interfaces with the deep and dark web.
- Structured Governance: Clear definition of standards, responsibilities, and procedures related to exposure, communication, and incident response regarding leaks and threats from anonymous networks.
- Compliance Monitoring: Implementation of secure information systems, centralized risk information capture, identification, blocking, and immediate treatment in case of non-compliance detection.
- Organizational Capacity Building: Establishment of training programs and knowledge dissemination, aligned with best practices in security, privacy, and data integrity in critical virtual environments.
The systemic adoption of these measures mitigates not only operational and reputational impacts but also ensures compliance with national and international digital governance standards.
Frequently Asked Questions
No, accessing the Dark Web is not a crime, but accessing or participating in illicit activities (buying/selling drugs, stolen data, etc.) is illegal. The risk lies in the content and the purpose of the access.
Yes, with advanced monitoring tools and traffic control policies, companies can identify access attempts or suspicious traffic related to the Dark Web.
Access should only be done by specialists, using isolated systems, without sensitive data, and never with personal or corporate credentials.
No. It is used for anonymity, privacy, freedom of expression, investigative journalism, among other legitimate purposes.
Conclusion
The technical analysis of the Dark Web reveals a highly complex environment, guided by advanced anonymization protocols, decentralized architecture, and strong resilience to surveillance and blocking. Access to these environments requires not only knowledge of software and networks but also a conscious posture towards corporate, operational, legal, and compliance risks. The thin line between legitimate and illicit uses reinforces the need for robust governance policies, advanced monitoring tools, emergency procedures, and constant team training.
For engineering, corporate security, and critical infrastructure projects, the implications go beyond technology choices: they involve broad understanding of threats, defense mechanisms, and applicable regulations. Commitment to structured audit practices, vulnerability analysis, and training enables the transformation of risk into competitive advantage through a proactive posture against the ecosystem of emerging threats and challenges.
Final Considerations
An in-depth understanding of the technical characteristics, risks, and best mitigation practices related to the Dark Web constitutes an essential step for information security and the soundness of business operations in the digital society. A3A Systems Engineering thanks you for reading this article and encourages professionals and companies to prioritize protection strategies and continuous monitoring of cyber risks.
Want to know how A3A Engineering solutions can help your company?
Discover the best Digital Security solutions in compliance with the LGPD.
To receive updated information and reference content, follow our official channels on social media and stay ahead in the security and applied engineering landscape.
Normative References
“ABNT NBR ISO/IEC 27001 — Information Security Management”
“ABNT NBR ISO/IEC 27005 — Risk Management”
“LGPD — General Data Protection Law”
“CERT.br — Center for Studies, Response and Treatment of Security Incidents in Brazil”
“NIST Cybersecurity Framework“
Relevant Links (Complementary Technical Materials)
What is the NIST Cybersecurity Framework?
What is Deep Web: Everything you need to know about the hidden side of the Internet
Corporate Compliance: Technical Definition, Benefits and Implementation Strategies

