In this article, we explore in detail the main concepts of the Access Control System, as well as covering best practices for its implementation.
Check it out!
Access Control is the set of methods, technologies, and procedures used to restrict, allow, or record the access of people and devices to physical environments or digital resources. The concept of this system is to ensure that only authorized users have access to sensitive locations or data, promoting security and traceability.
In this article, we will explore the main concepts and technologies of Access Control, as well as present best practices for its implementation.
Check it out!
[elementor-template id=”24446″]
What is Access Control?
Access control is the set of policies, procedures, equipment, and technologies designed to manage and regulate the access of people, vehicles, devices, or systems to physical environments or digital resources.
An Access Control System is designed to ensure that only properly authorized individuals or entities can access sensitive areas, equipment, or information, protecting assets and guaranteeing traceability.

Historically, access control was performed manually, using mechanical methods such as conventional keys and locks, identification cards, or physical sign-in sheets.
With advances in technology and growing demands for security and operational efficiency, electronic and digital solutions emerged, based on proximity cards, passwords, biometrics, and, more recently, mobile credentials and multi-factor authentication.
This evolution enabled the development of increasingly robust, integrated systems capable of providing detailed reports, routine automation, and integration with other security systems, such as video surveillance, intrusion alarms, and fire detection.

Digital transformation and the need for compliance in corporate and industrial environments have also driven the adoption of logical access controls, applied to systems, networks, applications, and databases, extending the concept beyond the physical environment and making it an essential part of modern information security strategies.
How Does an Access Control System Work?
Every efficient access control system is based on four fundamental principles that guide its architecture, configuration, and operation:
Fundamental Principles
What?
Defines which resources or areas are subject to control. This can be a room, a laboratory, a data center, a parking lot, a confidential file, or even a digital system or application.
Who?
Identifies who the users or entities requesting access are. These may include employees, visitors, service providers, vehicles, or even IoT devices in automated environments. Identification can be performed through physical credentials (cards, tags), digital credentials (login, certificate), or biometric credentials (fingerprint, facial recognition).
Where?
Specifies at which access points or geographic locations restrictions must be applied. This includes doors, gates, turnstiles, barriers, elevators, IT racks, and distributed systems across different locations.
When?
Determines during which periods or time windows access is permitted. This can be configured by work shifts, days of the week, holidays, maintenance windows, or even exceptional conditions such as emergency periods or lockdowns.
These four elements are programmed and managed through policies defined in the access control system, enabling the creation of detailed rules such as: “Only IT department employees may access the server room between 8 AM and 8 PM on business days, subject to biometric authentication.” In this way, access control acts as a defense and management mechanism, aligning physical and logical security with the operational and regulatory needs of each environment.
An access control system operates based on the identification, authentication, authorization, and logging of entry or exit attempts in restricted areas or digital resources. The basic workflow can be described in four main steps:
- Identification:
The user presents their credential to the system, which may be a proximity card, password, token, biometric data (fingerprint, facial, iris), or a mobile device. In digital environments, identification occurs via login, digital certificate, or device authentication. - Authentication:
The system verifies the authenticity of the presented credential, validating whether the card, password, or biometric data matches a previously authorized record. Authentication can be single-factor, two-factor, or multi-factor, increasing security levels according to the sensitivity of the environment. - Authorization:
Once authenticated, the system verifies whether that user has permission to access the requested resource or area at that specific time and location. This verification takes into account configured rules such as permitted time windows, access groups, hierarchical levels, enabled locations, and special conditions. - Logging and Action:
All access attempts — whether authorized or denied — are recorded in the system logs. If access is authorized, the system activates the release mechanism (for example, unlocks a door, releases a turnstile, grants digital access). If the attempt is denied, it may issue alerts to operators or administrators and maintain the access block.
This workflow enables full traceability, report generation, access pattern analysis, and rapid response to anomalous situations.
Types of Access Control
Access control can be classified into two major groups: physical access control and logical access control. Both share the same principles of authentication, authorization, and logging, but differ in the nature of the protected resources and the methods of enforcement.
Physical Access Control
Physical access control encompasses all mechanisms, procedures, and technologies designed to restrict or permit the entry of people, vehicles, or equipment into specific physical spaces, such as buildings, technical rooms, industrial areas, data centers, and critical environments.
In this context, a combination of physical barriers — such as doors, turnstiles, and gates — is used alongside identification devices, such as card readers, biometric sensors, or mobile device authentication.
The purpose is to protect people, assets, and sensitive information against risks of intrusion, theft, or sabotage, while ensuring the traceability of all movements.
Physical access control systems typically operate in an integrated manner with video surveillance, alarms, and other security subsystems, enabling detailed rules for time windows, user profiles, and different authorization levels.
Logical Access Control
Logical access control is the discipline focused on protecting digital assets, managing who can access systems, networks, applications, files, databases, or IT resources. The objective is to ensure the confidentiality, integrity, and availability of information, preventing unauthorized access, data leaks, and cyberattacks.
To achieve this, it employs mechanisms such as login and password authentication, multi-factor authentication, digital certificates, tokens, and biometrics. Permission policies are established based on user profiles, groups, roles, or attributes, and can be implemented on local servers, cloud environments, or corporate networks.
Logical control is complemented by monitoring and auditing systems that record access attempts, identify anomalies, and enable rapid responses to security incidents.
In organizational environments, the integration of physical and logical control is increasingly common, aiming for comprehensive asset protection, regulatory compliance, and efficient governance over critical access.
Authentication Principles and Factors
Something you know (passwords, PINs)
Something you have (cards, mobile devices)
Something you are (biometrics)
Single-factor, two-factor, and multi-factor authentication
Access Credentials
Access Cards
Proximity cards are widely used in corporate, industrial, and institutional environments. They use radio frequency (RFID) technology for contactless communication between the card and the reader, offering convenience and speed in authentication.
Proximity Cards
Smart Cards
Biometrics
Mobile Credential
System Devices and Components
Readers and controllers
Actuators
Peripherals and sensors
Communication interfaces (Wiegand, OSDP, RS485, TCP/IP)
Access Control System Architectures
Centralized systems
Distributed systems
Access Control Project
The Evolution of Technology in Access Control
Technological advancement has played a fundamental role in the evolution of access control. New trends and innovations have made it possible to identify and authenticate individuals in more efficient and secure ways.
For example, Facial Recognition and Biometrics are technologies that are becoming increasingly common in the access control field. These solutions offer higher levels of accuracy and convenience, providing a more agile and robust access experience.
Another example is License Plate Recognition (LPR), which is already a reality in many developments. This technology enables the quick identification and recording of vehicles entering and exiting specific locations, enhancing security and access control. The data captured by LPR cameras can be used for various purposes, ranging from parking lot management to the enforcement of traffic restrictions, such as identifying whether a vehicle has been stolen or has outstanding administrative penalties.
Access Control is becoming more integrated and connected to other systems and devices. Internet of Things (IoT) technology plays an important role in this regard, enabling the interconnection of different devices and the real-time exchange of information.
This allows for greater automation and intelligence in access control systems, making them more effective and adaptable to the specific needs of each environment.
What are the Types of Access Control Systems
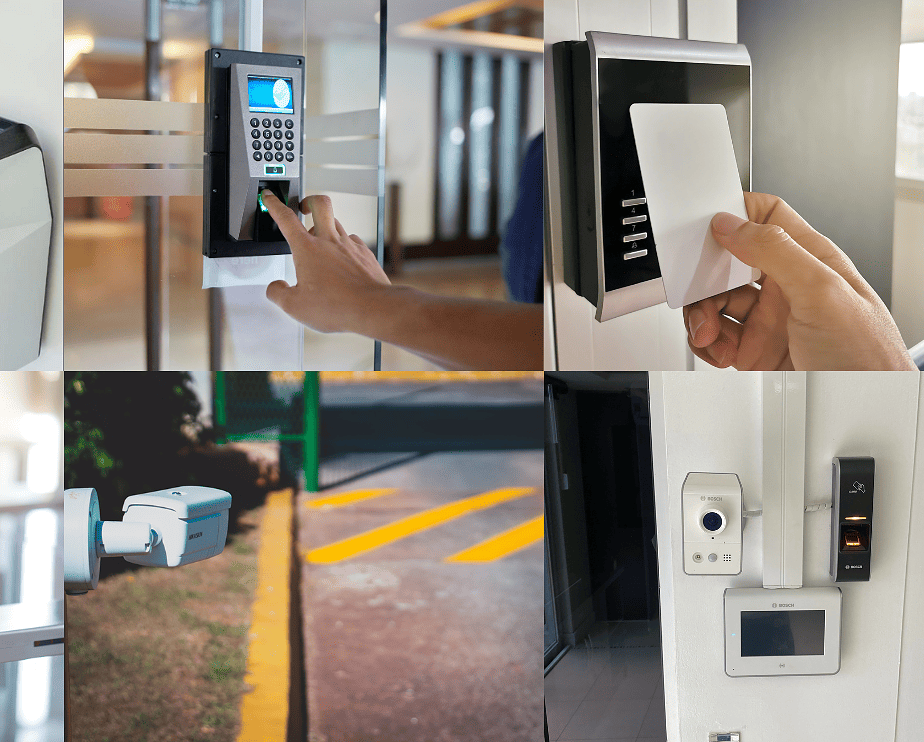
There are several types of physical Access Control systems, each with its own purpose and suitability for different environments. These systems use advanced technologies to monitor and manage the access of individuals to specific areas, providing effective security and control.
The equipment and devices used for Access Control are selected according to the specific needs of the environment and what must be monitored, whether vehicles or people. Each type of device has distinct characteristics and security levels, offering a variety of options to ensure adequate protection and control.
Below, we present the main types of physical Access Control Systems currently in use:
Biometric Terminals
Biometrics is a technology that uses unique and measurable characteristics of living beings to identify and authenticate the identity of individuals.
The use of biometrics in access control systems provides a highly secure and reliable way to ensure that only authorized individuals have access to certain areas or information.
Below, we will detail some of the main biometric methods used in Access Control Systems:
Hand Geometry
Hand Geometry Recognition technology is a biometric method used in Access Control Systems to authenticate a person’s identity based on the unique characteristics of the palm of the hand.
This method is based on the analysis of the “geometric” characteristics of the hand, such as length, width, the position of the joints, and other distinctive elements.
In the hand geometry authentication process, a biometric device, such as a scanner or image sensor, is used to capture the image of the user’s palm.
This image is processed by image processing algorithms, which identify the relevant characteristics, such as main lines — like the palm line and the finger lines — as well as reference points, such as joints and characteristic curves.
Based on the extracted characteristics, a reference model of the user’s hand geometry is built and stored in a secure database. This model serves as a unique and exclusive representation of the user’s palm. During the authentication process, the user’s palm is captured again and its characteristics are compared with the stored reference model.
Hand geometry recognition technology offers advantages in terms of accuracy and security. Hand geometry is a highly distinctive characteristic that is difficult to falsify, which increases the reliability of the Access Control System. In addition, the authentication process is fast and does not require direct physical contact, which is especially relevant in environments that require hygiene and social distancing.

Fingerprint Reading
Fingerprint reading is a biometric technology widely used in Access Control Systems to authenticate a person’s identity based on the unique characteristics of their fingerprints. This technology is based on the analysis of the patterns formed by the fingerprints present on the surface of the fingertips.
During the authentication process, the user’s fingerprints are compared with previously registered fingerprints. If there is a match within an acceptable similarity threshold, the user’s identity is verified and access is granted.

Facial Recognition
Facial Recognition is an advanced biometric technology that uses algorithms to analyze and identify unique facial characteristics of an individual. This technology enables identity authentication based on facial attributes, such as the shape of the face, the arrangement of the eyes, nose, mouth, and other distinctive features.
To perform facial recognition, a biometric device captures the image of the user’s face. The system then executes a series of steps to extract and analyze facial reference points, such as the contour of the lips, the position of the eyes, nose, and other important details.
These reference points are converted into a set of digital data, which can be compared against a database of previously registered faces. During authentication, the system performs a match between the captured face data and the stored data, searching for similarities or corresponding patterns.
There are different approaches to facial recognition, such as recognition based on 2D facial features and 3D recognition, which takes into account the depth and three-dimensional structure of the face. In addition, machine learning algorithms are frequently used to improve the accuracy of facial recognition, allowing the system to adapt and refine its matches over time.

Voice Recognition
Voice recognition is a biometric technology that uses the unique characteristics of an individual’s voice to authenticate their identity. This technology is based on exclusive vocal patterns and characteristics, such as intonation, rhythm, frequency, and other aspects related to speech.
To perform voice recognition, a biometric device, such as a microphone, captures the user’s voice. The system then converts the audio signal into digital data, which is processed and analyzed to extract the relevant vocal characteristics.
Voice recognition algorithms compare these extracted characteristics with voice samples previously registered in a database. During the authentication process, the system searches for similarities or corresponding patterns, determining whether the captured voice matches the registered user’s voice.
Voice recognition can be implemented in different ways, depending on the context of use. It can be used in physical access control systems, where the user must speak a specific phrase to authenticate their identity. It can also be applied in mobile device authentication systems, where the user’s voice is compared with information stored on the device.
Monitoring-Based Systems
Monitoring-based access control systems are an effective approach to ensuring the security and control of restricted areas.
These systems use strategically positioned surveillance cameras to monitor and capture relevant information in real time. With the aid of advanced algorithms, these systems can perform the recognition and analysis of different elements, enabling automated authentication and activity logging:
License Plate Recognition (LPR)
License plate reading, also known as LPR (License Plate Recognition), is a technology used to automatically identify and capture the information contained on vehicle license plates. This monitoring-based access control system uses surveillance cameras and advanced algorithms to recognize and process license plates in real time.
LPR is capable of reading and interpreting the alphanumeric characters present on vehicle license plates, regardless of the speed at which they are moving. To do this, cameras specialized in LPR are positioned in strategic locations, such as parking lot entrances and exits, access gates, public roads, and others.
Upon capturing the image of the vehicle’s license plate, the license plate reading system performs a series of steps to identify and extract the characters from the plate. This includes segmentation processes, where the plate is separated from the rest of the image, and recognition processes, where the characters are analyzed and compared against a database containing registered plates.
License plate recognition algorithms use image processing techniques and machine learning to perform the analysis and recognition of characters. These algorithms can be trained with a large number of examples of license plates of different models and variations, improving the system’s accuracy over time.

Remote Gatehouse
The remote gatehouse is a monitoring-based access control system that allows remote viewing, communication, and authorization of access to a given location. Unlike a conventional gatehouse, where a security guard is physically present, the remote gatehouse uses communication technology and surveillance cameras to manage and control access remotely.
In this system, surveillance cameras are installed at the entrance and exit areas of the location, as well as at other strategic points to ensure broad coverage. These cameras capture images in real time and transmit them to a remote monitoring center.
At the monitoring center, qualified operators analyze the received images, identify the people or vehicles wishing to access the location, and communicate via audio and video intercoms. Communication can be carried out through both voice calls and video conferences, enabling identity verification and access authorization.
Proximity Cards
Proximity cards are devices used in physical access control systems that contain a pre-programmed chip inside. Each card has a unique identification number, making it one-of-a-kind in its identity.
The operation of these cards is based on the proximity between the card and a specific reader. When the card is brought close to the reader, the chip inside the card transmits its identification number to the reader, which in turn sends this information to software responsible for access control.
The software then verifies the user’s identity based on the card’s identification number. If the identity is recognized, access is granted, allowing the user to enter the controlled environment. Otherwise, if the identity is not recognized or the card has been deactivated, access is denied and the user is prevented from entering.

Password or PIN
Physical access control systems based on passwords and PINs are widely used to authenticate and authorize access to restricted physical environments, such as buildings, rooms, or specific areas. These systems work by requesting a password or PIN code from users, who must enter it on a keypad or panel to verify their identity.
The advantages of password and PIN systems include their simplicity and ease of use. Users are familiar with the concept of passwords and PIN codes, making adoption and interaction with the system more intuitive. In addition, the implementation of these systems is relatively cost-effective, as it requires only an input device (such as a keypad) and access control software.
Another advantage is flexibility. Password and PIN systems allow users to define their own passwords or PIN codes, giving them a sense of control and personalization. Furthermore, passwords and PIN codes can be changed easily, making them useful in scenarios where access needs to be updated regularly, such as when an employee leaves the organization.
However, password and PIN systems also present significant disadvantages and vulnerabilities. The primary concern is security. Passwords and PIN codes can be easily compromised if they are weak or predictable. Many users tend to choose passwords that are easy to guess, such as birth dates, family members’ names, or simple numeric sequences. This makes these systems vulnerable to brute-force attacks or password guessing, where an attacker tries multiple combinations until finding the correct one.

Mobile Device-Based Systems
Mobile device-based access control systems represent an innovative technological solution that enables the authentication and authorization of access to physical environments or resources through smartphones and tablets.
One of the main advantages of these systems is their remarkable convenience for users. Mobile devices have become widely available and easily accessible, making authentication through them a practical and intuitive option. Furthermore, the mobility of devices allows users to authenticate themselves in different locations, eliminating the need to carry physical cards or keys.
This technology uses customized mobile applications that allow users to carry out authentication processes with ease. Through secure connections and encrypted communication protocols, mobile devices communicate with access control systems, providing the information necessary to verify the user’s identity and grant or deny access.

The Implementation of an Access Control Project
The implementation of an access control project is a fundamental step in ensuring the safety and protection of environments, whether residential, commercial, or industrial. This process involves a series of activities and measures to establish an efficient system for controlling the entry and exit of people, vehicles, and objects.
The first step in implementing the access control project is conducting a detailed analysis of the needs and characteristics of the environment in question. This involves identifying critical access points, restricted areas, people and vehicle flows, as well as specific security requirements. Based on this analysis, it is possible to determine the most appropriate technological solutions and the security measures to be implemented.
Once the requirements have been defined, the next step is to select the necessary access control equipment and systems. This may include the installation of security cameras, biometric readers, turnstiles, automated doors, card or tag identification systems, among other devices. It is important to choose reliable products and technologies that meet security standards and are compatible with the needs of the environment.
After acquiring the equipment, it is time to carry out the physical installation and integration of the systems. Access control devices must be installed in strategic locations in accordance with the established project. In addition, it is necessary to configure the software and database systems to manage access information and ensure correct user authentication.
Another crucial aspect of implementing the access control project is the definition of security policies and procedures. This includes establishing clear guidelines on who is granted access, permitted hours, identification and authentication rules, among other measures. It is also important to provide adequate training to users and staff so that they know how to correctly use the system and follow the established security policies.
After the implementation is complete, it is essential to conduct tests and evaluations to ensure that the access control system is functioning properly and meeting security expectations. It is advisable to perform periodic audits and maintain continuous monitoring to identify possible failures or vulnerabilities and take the necessary corrective measures.
Access Control System Applications
Access control systems have a wide range of applications across various sectors, including businesses, government institutions, healthcare facilities, airports, data centers, and many others.
Their implementation plays a crucial role in preventing unauthorized intrusions, protecting restricted areas and sensitive resources, ensuring compliance with security and privacy regulations, and efficiently managing the flow of people in high-traffic locations.
These systems offer an advanced and reliable approach to controlling the access of individuals, vehicles, and objects to specific environments. They can be integrated with other security systems, such as video surveillance systems and alarms, to provide a comprehensive and effective approach to protection and monitoring.
Main Benefits of Access Control
Implementing an access control system brings a number of advantages, with security certainly being the primary one, although not the only one. Below, we present the main benefits of this system:
Better Environment Management: Access control systems enable more efficient environment management, ensuring that only authorized individuals have access to specific areas. This helps prevent unwanted situations and ensures the security of resources and information.
Support for Decision-Making: With accurate records of access activities, access control systems provide valuable information for decision-making. The data can be analyzed to identify patterns, trends, and behaviors, assisting in the implementation of more effective security measures.
Restriction of access for employees and unauthorized individuals: Access control systems make it possible to restrict access for employees and unauthorized individuals to specific locations. This prevents unauthorized access to restricted areas, such as server rooms, confidential file rooms, or production areas.
Reduction of costs associated with hiring security professionals: By implementing efficient access control systems, organizations can reduce their reliance on physical security professionals. Automated systems play a key role in monitoring and controlling access, thereby reducing operational costs.
Fast and agile employee access to environments: Access control systems allow employees to quickly access the areas and resources needed to carry out their tasks. This improves operational efficiency and avoids unnecessary delays.
Creation of access lists for internal events: Access control systems facilitate the creation of access lists for internal events, such as conferences, training sessions, or meetings. This ensures that only authorized individuals can attend these events, enhancing security and control.
Quick location of employees: By integrating access control systems with location technologies, it is possible to quickly locate employees in the event of an emergency or urgent communication need.
Control of the number of people in environments: Access control systems allow organizations to control and monitor the number of people present in certain environments. This is particularly useful in locations with limited capacity, such as meeting rooms, auditoriums, or event areas.
Behavioral analysis of employees and vendors: Access control systems can provide valuable information about the behavior of employees and vendors. This includes time spent in the environment, access schedules, and activity history. This behavioral analysis can help detect unusual patterns and identify potential threats.
Visitor identification and visit frequency logging: Access control systems allow organizations to identify and register visitors, ensuring the security of both information and people. This is particularly important in environments with restricted or confidential access.
Conclusion
In summary, access control systems play a fundamental role in the security and protection of resources and information across various environments. They provide an essential layer of protection, enabling organizations to restrict access only to authorized individuals and ensure the integrity of their operations.
Furthermore, access control systems ensure compliance with security and privacy regulations, record visitor frequency and visits, and provide a comprehensive view of the environment, enabling better security management and a more effective response to incidents.
However, it is important to emphasize that the implementation of access control systems must be carefully planned and executed, taking into account the specific needs of the organization and the most appropriate technologies. Choosing reliable and scalable solutions, as well as adopting least privilege practices, are essential to achieving the best results and ensuring the effectiveness of the system.

